Offensive and defensive cybersecurity solutions in healthcare
Abstract
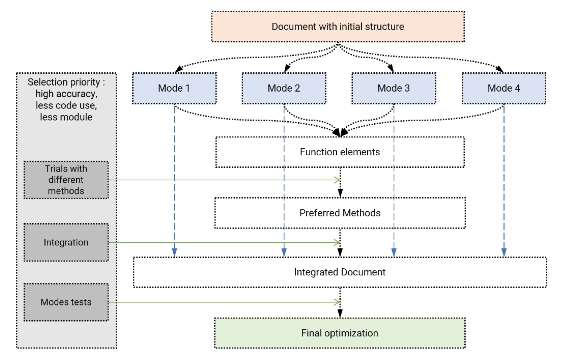
Healthcare services usually implement defensive data strategies; however, offensive data strategies offer new opportunities because they focus on improving profitability or revenues. Offensive data also helps develop new medicine, diagnosis, and treatment due to the ease of data-sharing rather than data control or other restrictions. Balancing defensive data and offensive data is balancing data control and flexibility. It is a challenge to keep a balance between the two. Sometimes, it is necessary to favor one over the other, depending on the situation. A robust cybersecurity program is contingent on the availability of resources in healthcare organizations and the cybersecurity management staff. In this paper, a cybersecurity system with the functions of both defensive cybersecurity and offensive cybersecurity in a medical center is proposed based on big data, artificial intelligence (AI)/machine learning (ML)/deep learning (DL).
Copyright (c) 2025 Author(s)

This work is licensed under a Creative Commons Attribution 4.0 International License.
References
[1]Dumitrescu B. Operationalising Cyberspace–From Cyber Security to Operational Success. Romanian Military Thinking. 2019; (1): 50–73.
[2]Rains T. Cybersecurity Threats, Malware Trends, and Strategies: Learn to mitigate exploits, malware, phishing, and other social engineering attacks. Packt Publishing Ltd; 2020.
[3]Buchanan B. A national security research agenda for cybersecurity and artificial intelligence. Center for Security and Emerging Technology. 2020. doi: 10.51593/2020ca001
[4]Sarker IH. Multi‐aspects AI‐based modeling and adversarial learning for cybersecurity intelligence and robustness: A comprehensive overview. Security and Privacy. 2023; 6(5). doi: 10.1002/spy2.295
[5]Kumar N, Aggarwal D. LEARNING-based Focused WEB Crawler. IETE Journal of Research. 2023; 69(4): 2037–2045. doi: 10.1080/03772063.2021.1885312
[6]Zhang Wu M, Luo J, Fang X, et al. Modeling multivariate cyber risks: Deep learning dating extreme value theory. Journal of Applied Statistics. 2021; 50(3): 610–630. doi: 10.1080/02664763.2021.1936468
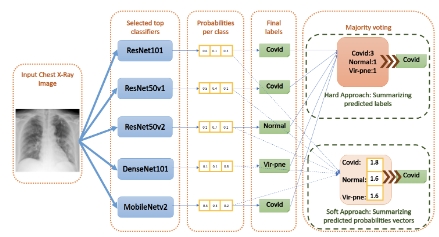
[7]Kumar N, Hashmi A, Gupta M, et al. Automatic diagnosis of Covid-19 related pneumonia from CXR and CT-Scan images. Engineering, Technology & Applied Science Research. 2022; 12(1): 7993–7997. doi: 10.48084/etasr.4613
[8]Ajmal AB, Shah MA, Maple C, et al. Offensive security: Towards proactive threat hunting via adversary emulation. IEEE Access. 2021; 9: 126023–126033. doi: 10.1109/access.2021.3104260
[9]DalleMule L, Davenport TH. What’s your data strategy. Harvard Business Review. 2017; 95(3): 112–121.
[10]Kumar N, Kundu A. Cyber security focused deepfake detection system using big data. SN Computer Science. 2024; 5(6): 752. doi: 10.1007/s42979-024-03105-8
[11]Kumar N, Kundu A. SecureVision: Advanced Cybersecurity Deepfake Detection with Big Data Analytics. Sensors. 2024; 24(19): 6300. doi: 10.3390/s24196300
[12]Ligo AK, Kott A, Linkov I. How to measure cyber-resilience of a system with autonomous agents: Approaches and challenges. IEEE Engineering Management Review. 2021; 49(2): 89–97. doi: 10.1109/emr.2021.3074288
[13]Yamin MM, Ullah M, Ullah H, et al. Weaponized AI for cyber attacks. Journal of Information Security and Applications. 2021; 57: 102722. doi: 10.1016/j.jisa.2020.102722
[14]Michael JB, Wingfield TC. Defensive AI: The future is yesterday. Computer. 2021; 54(9): 90–96. doi: 10.1109/mc.2021.3092480
[15]Malatji M, Tolah A. Artificial intelligence (AI) cybersecurity dimensions: A comprehensive framework for understanding adversarial and offensive AI. AI and Ethics. 2024; 1–28. doi: 10.1007/s43681-024-00427-4
[16]Macas M, Wu C, Fuertes W. Adversarial examples: A survey of attacks and defenses in deep learning-enabled cybersecurity systems. Expert Systems with Applications. 2024; 238: 122223. doi: 10.1016/j.eswa.2023.122223
[17]Uriawan W, Adriansyah S, Maulidiyah SJ, et al. Challenges and opportunities: Improve patient data security and privacy in distributed systems. 2024. doi: 10.20944/preprints202407.0163.v1
[18]Yu M, Zhuge J, Cao M, et al. A survey of security vulnerability analysis, discovery, detection, and mitigation on IoT devices. Future Internet. 2020; 12(2): 27. doi: 10.3390/fi12020027
[19]Alsubaei F, Abuhussein A, Shiva S. Security and privacy in the internet of medical things: Taxonomy and risk assessment. In: Proceedings of the 2017 IEEE 42nd Conference on Local Computer Networks Workshops (LCN Workshops); 9 October 2017; Singapore, Singapore. pp. 112–120.
[20]Taheri S, Asadizanjani N. An Overview of medical electronic hardware security and emerging solutions. Electronics. 2022; 11(4): 610. doi: 10.3390/electronics11040610